DO LESS IT, DO MORE BUSINESS
Tech Pros 360 BUSINESS
We provide customized solutions for your businesses, ensuring the most efficient and secure operations to meet your companies’ needs.

How We Work
Pick A STRATEGY
-
Why pick 1 when you can pick them all? Our service plans include everything you need to stay safe online with your own personal IT team.
-
Tip toe into safety and efficiency by starting small. You can select 1 or a few key services that are hindering your daily progress.
-
Our top-of-the-line security and remote support applications will fill in the hole for whatever deficit you’re experiencing.
Find the plan that’s right for your business
-
Basic
Endpoint Management
> Next-Gen Antivirus (NGAV)
> Endpoint Detection & Response (EDR)
> Remote Monitoring & Management (RMM)
-
Standard
User Management
> Cybersecurity Awareness & Phishing Training
> Dark Web Monitoring & Reporting
> Email Security & Anti-Phishing
> Cloud Detection & Response (CDR)
> Cloud Backup & Recovery
-

Premium
Risk Management
> Network Scanning & Discovery
> Vulnerability Management
> Penetration Testing
> Compliance & Risk Analysis
Cybersecurity & Software
-

Endpoint Backup
Secure device-level backups ensuring protection from critical data loss.
-
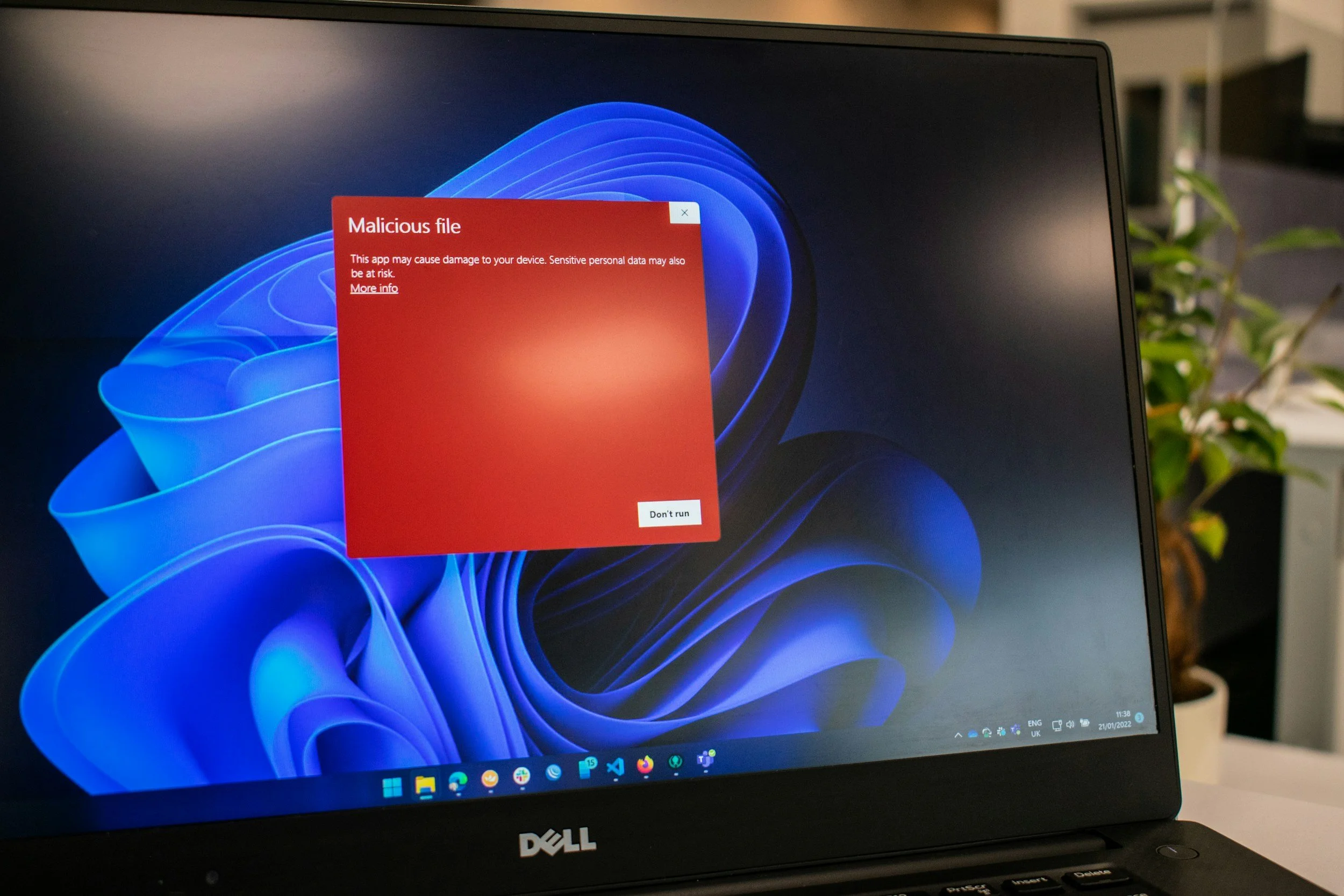
Next-Gen Antivirus (NGAV)
AI-driven protection to block emerging malware and viruses.
-

Endpoint Detection & Response (EDR)
Real-time device monitoring to contain and remediate zero-day threats.
-

Managed Detection & Response (SOC)
24/7 expert threat hunting and active breach response.
-

Remote Monitoring & Management (RMM)
Proactive endpoint monitoring to resolve issues before they impact.
-

Cybersecurity Awareness & Phishing Training
Continuous staff training to reduce human error and phishing.
-

Dark Web Monitoring & Reporting
Proactive alerts for stolen credentials and leaked sensitive data.
-

Email Security & Anti-Phishing
Advanced behavior analysis to stop sophisticated email-based threats.
-

Cloud Detection & Response (CDR)
Continuous security monitoring for SaaS applications and cloud data.
-

Cloud Backup & Recovery
Automated recovery systems for critical SaaS data and files.
-

Network Scanning & Discovery
Deep-dive scans to identify vulnerabilities and secure sensitive data.
-

Vulnerability Management
Systematic identification and resolution of security flaws across assets.
-

Penetration Testing
Simulated cyberattacks to validate and strengthen existing security controls.
-

Compliance & Risk Analysis
Regulatory reporting and documentation to track organizational security posture.
Technical Support
-

Remote Support
Expert help desk support delivered through secure remote access.
-

Onsite Support
Hands-on technical assistance for physical infrastructure and installs.
-

Cabling
Building network infrastructure and eliminating messy wiring.
-

Account Management
Strategic oversight of service accounts for cost and benefit optimization.
-

Computers
Complete workstation and server health, security, and maintenance.
-

Cloud
Secure and efficient management of your digital work environments.
-

Networks
Robust connectivity solutions for reliable and secure business operations.
-

Surveillance
Advanced physical security through integrated camera and access systems.
-

Phones
Reliable communication solutions for landline and cellular business needs.
-
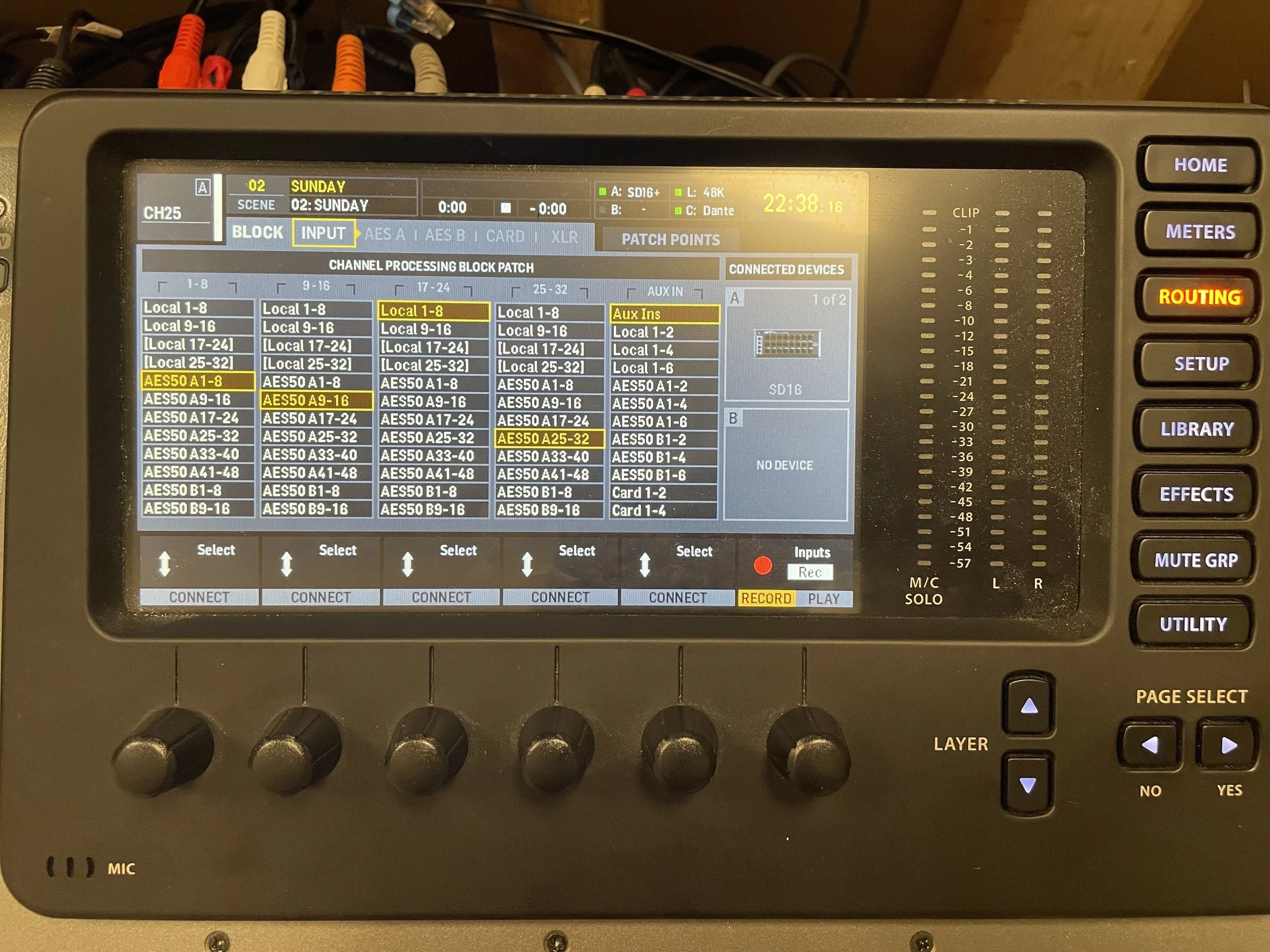
Audio
High-quality sound systems for immersive professional and commercial environments.
-

Visuals
Expert streaming, display, and multi-camera setups for visual impact.
Branding & Marketing
-

Channel Management
Active social media management to build brand awareness and loyalty.
-

Creative Media Production
High-impact visual asset creation through design, photo, and video.
-

Digital Advertising
Targeted ad campaigns to drive immediate traffic and conversions.
-

Email Campaigns
Strategic outreach to nurture relationships and drive customer retention.
-

Web Management
Performance optimization and maintenance for your central marketing hub.

